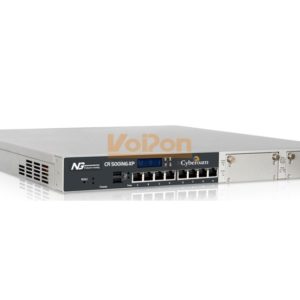
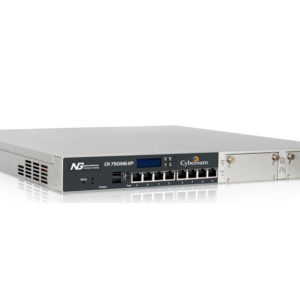
Interfaces
| Copper GbEPorts |
3 |
| Configurable Internal/DMZ/WANPorts |
Yes |
| Console Ports (RJ45) |
1 |
| USB Ports |
2 |
System Performance*
| Firewall Throughput (UDP) |
1,000 |
| Firewall Throughput (TCP) |
750 |
| New sessions/second |
3,500 |
| Concurrent sessions |
60,000 |
| IPSec VPN Throughput |
110 |
| No. of IPSec Tunnels |
50 |
| SSL VPN Throughput |
50 |
| Anti-Virus Throughput |
180 |
| IPS Throughput |
140 |
| UTM Throughput |
80 |
Stateful Inspection Firewall
– Layer 8 (User – Identity) Firewall
– Multiple Security Zones
– Access Control Criteria (ACC) – User – Identity, Source &Destination Zone,MACand IP address, Service
– UTM policies – IPS, Web Filtering, Application Filtering, Anti-Virus, Anti-Spam and Bandwidth Management
– Layer 7 (Application) Control & Visibility
-Access Scheduling
– Policy based Source & DestinationNAT
– H.323, SIPNATTraversal
– 802.1q VLAN Support
– DoS &DDoS attack prevention
-MAC&IP-MAC filtering and Spoof prevention
GatewayAnti-Virus & Anti-Spyware
-Virus,Worm,Trojan:Detection &Removal
– Spyware, Malware, Phishing protection
-Automatic virus signature database update
– Scans HTTP, HTTPS, FTP, SMTP, POP3, IMAP, IM, VPN Tunnels
– Customize individual user scanning
– Scan and deliver by file size
– Block by file types
-Add disclaimer/signature
Gateway Anti-Spam
– Inbound Scanning
– Real-time Blacklist (RBL), MIME header check
– Filter based on message header, size, sender, recipient
– Subject line tagging
– IP address Black list/White list
– Redirect Spam mails to dedicated email address
– Image-based Spam filtering usingRPDTechnology
– Zero hour Virus Outbreak Protection
– IP Reputation-based Spam filtering
– Spam notification through digest
Intrusion Prevention System
– Signatures: Default (4500+), Custom
– IPS Policies: Multiple, Custom
– User-based policy creation
-Automatic real-time updates from CRProtect networks
– ProtocolAnomaly Detection
-DDoS attack prevention
Web Filtering
– InbuiltWeb Category Database
– URL, keyword, File type block
– Categories: Default(82+), Custom
– Protocols supported: HTTP, HTTPS
– Block Malware, Phishing, Pharming URLs
– Schedule-based access control
– Custom block messages per category
– Block JavaApplets, Cookies,Active x
– CIPA Compliant
– Data leakage control via HTTP, HTTPS upload |
Application Filtering
– Inbuilt Application Category Database
– Application Categories: e.g. Gaming, IM, P2P,
Proxy
– Spam notification through digest DDoS attack prevention 11+
– Schedule-based access control
– Block
– P2Papplications e.g. Skype
-Anonymous proxies e.g. UItra surf
– “Phone home” activities
– Keylogger
– Layer 7 (Applications) & Layer 8 (User – Identity) VisibilityVirtual Private Network
– IPSec, L2TP, PPTP
– Encryption – 3DES, DES, AES, Twofish, Blowfish, Serpent
– HashAlgorithms – MD5, SHA-1
-Authentication – Preshared key, Digital certificates
– IPSecNATTraversal
– Dead peer detection and PFS support
– Diffie Hellman Groups – 1,2,5,14,15,16
– External Certificate Authority support
– Export RoadWarrior connection configuration
– Domain name support for tunnel end points
-VPNconnection redundancy
– Overlapping Network support
– Hub &SpokeVPNsupport
SSL VPN
-TCP&UDPTunneling
– Authentication – Active Directory, LDAP, RADIUS, Cyberoam
– Multi-layered Client Authentication – Certificate, Username/Password
– User &Group policy enforcement
– Network access – Split and Full tunneling
– Browser-based (Portal)Access – Clientless access
– Lightweight SSLVPNTunneling Client
– Granular access control to all the Enterprise Network resources
– Administrative controls – Session timeout, Dead Peer Detection, Portal customization
– TCP- based Application Access – HTTP, HTTPS, RDP, TELNET, SSH
Instant Messaging (IM) Management
-Yahoo and Windows Live Messenger
-Virus Scanning for IM traffic
-Allow/Block Login
-Allow/Block FileTransfer
-Allow/BlockWebcam
-Allow/Block one-to-one/group chat
– Content-based blocking
– IM activities Log
-Archive files transferred
– CustomAlerts
WirelessWAN
-USBport 3G/4G and Wimax Support
– PrimaryWANlink
-WANBackup link
Bandwidth Management
– Application and User Identity based Bandwidth Management
– Guaranteed &Burstable bandwidth policy
– Application &User Identity basedTraffic Discovery
– MultiWANbandwidth reporting
– Category-based bandwidth restriction
User Identity and Group Based Controls
-Access time restriction
-Time and Data Quota restriction
– Schedule based Committed and Burstable Bandwidth
– Schedule based P2Pand IM Controls
Networking
– Failover – Automated Failover/Failback, Multi-WAN failover, 3GModem failover
-WRRbased load balancing
– Policy routing based onApplication and User
– IP Address Assignment – Static, PPPoE, L2TP, PPTP & DDNS Client, Proxy ARP, DHCP server, DHCP relay
– Support for HTTPProxy
– Dynamic Routing: RIP v1& v2, OSPF, BGP, Multicast Forwarding
– Parent Proxy support withFQDN
– “IPv6 Ready” Gold Logo |
Administration & System Management
-Web-based configuration wizard
– Role-based access control
– Firmware Upgrades viaWeb UI
-Web 2.0 compliant UI (HTTPS)
– UI Color Styler
– Command Line Interface (Serial, SSH,Telnet)
-SNMP(v1, v2c, v3)
– Multi-lingual support: Chinese, Hindi, French, Korean
– Cyberoam Central Console (Optional)
– NetworkTime Protocol Support
User Authentication
– Internal database
-Active Directory Integration
-Automatic Windows Single Sign On
– External LDAP/RADIUS database integration
– Thin Client support – Microsoft Windows Server 2003 Terminal Services and Citrix xenApp – Novell eDirectory
-RSASecurID support
– ExternalAuthentication – Users andAdministrators
– User/MAC Binding
– MultipleAuthentication servers
Logging/Monitoring
– Graphical real-time and historical monitoring
– Email notification of reports, gateway status, viruses and attacks
– Syslog support
– Log Viewer – Firewall, IPS,Web filter, Anti Virus, Anti Spam,Authentication, System andAdmin Events
IPSecVPNClient**
– Inter-operability with major IPSecVPNGateways
– Supported platforms: Windows 2000, WinxP 32/64- bit, Windows 2003 32-bit, Windows 2008 32/64-bit, Windows Vista 32/64-bit, Windows 7 RC1 32/64-bit
– Import Connection configuration
Certification
– ICSAFirewall – Corporate
– CheckmarkUTMLevel 5 Certification
-VPNC- Basic andAESinteroperability
– “IPv6 Ready” Gold Logo
Hardware Specifications
| Memory |
1GB |
| Compact Flash |
4GB |
Compliance
-CE
-FCC
Dimensions
| HxWxD(inches) |
1.7 x 6 x 9.1 |
| HxWxD(cms) |
4.4 x 15.3 x 23.2 |
| Weight |
1.5 kg, 3.307 lbs |
Power
| Input Voltage |
100-240 VAC |
| Consumption |
13.2W |
| Total Heat Dissipation (BTU) |
45 |
Environmental
| operating temperature |
0 to 40 °C |
| Storage Temperature |
-25 to 75 °C |
| Relative Humidity (Non condensing) |
10 to 90% |
|